Opinion
Counting The Cost Of BYOD
There are many pro’s and con’s when actioning a Bring Your Own Device to work policy and these effect both employee and employer. When counting the cost of BYOD it is important to recognize both financial and psychological factors:
Productivity vs Stress
When BYOD systems are put in place it has been clearly demonstrated that productivity is increased. According to Cisco, the simple implementation of using a smartphone or tablet that is familiar to the employee leads to better productivity, saving on average 81 minutes of time performing tasks each week.
6 Benefits of a Java CMS
Java. You can’t beat the classic when it comes to development languages for an enterprise-level content management system (ECM). Compared to .NET, PHP, or C# Java is still the top development language for its reliability, stability and suitability for “building back-ends for modern enterprise-web applications. With Java and frameworks based on it, web developers can build scalable web apps for a variety of users.”
What is the Weakest Link in Network Security?
The landscape of network security and criminal behavior continues to evolve at an astonishing rate, and for the average company this is going to mean at least a handful of risks that must be addressed immediately. For those that have taken all of the traditional steps for protecting their network and their company's information, it may be surprising to hear that they still have vulnerable points in their system. Within most companies, the number one threat is not going to be a dedicated attack against a firewall or a backdoor hack into one's software, it is going to be the authorized users themselves.
BYOD Red Alert: Employees are Your Biggest BYOD Security Threat
With news of security breaches happening at major corporations all over the world, it’s easy for business leaders to start focusing all of their attention on outside threats. Hackers seem to be everywhere these days, so a strategy that heightens network security against cyber attacks is usually a good idea. If your business has adopted bring your own device (BYOD) policies, however, all that preparation for avoiding outside risks may be misdirected.
A Skeptical Forecast for Wearable Tech
At the beginning of 2014, a lot of people predicted it would be the year wearable technology really broke through. The promises of Google Glass and rumors of Apple Watch exited us, and we could already see the success of things like fitness bands. However, as the year is coming to a close, we now realize we were a little presumptuous. In fact, we can’t even be sure 2015 will be the year for wearables. There’s a lot of promises and hype surrounding wearable devices, but a closer look at their current popularity leaves their future up for debate.
6 Ways Small Businesses Can Improve Network Security
It’s amazing the influence technology has. All these new gadgets have made our lives easier in so many ways, but they have also dramatically changed the cultures that embrace them. For example, digital theft is becoming a more common threat than physical theft.
We’ve heard examples of large corporations having their customer information hacked, or even celebrities having their personal photos stolen. And while we think criminals would only go after the big guys, small businesses aren’t in the clear. Without massive IT budgets and industry professionals, their networks are often left unprotected and become easy targets for intruders.
How Apple Pay Differs From Other Mobile Payment Services
You better get used to paying with your phone. It’s already a popular method of making purchases in places like Japan and even some countries in Africa, but in the United States it hasn’t caught on quite as quickly. While so-called tap-to-pay methods have been around for a number of years already, Apple’s recent announcement of their own mobile payment service, called Apple Pay, has sent a new wave of excitement through the technology community.
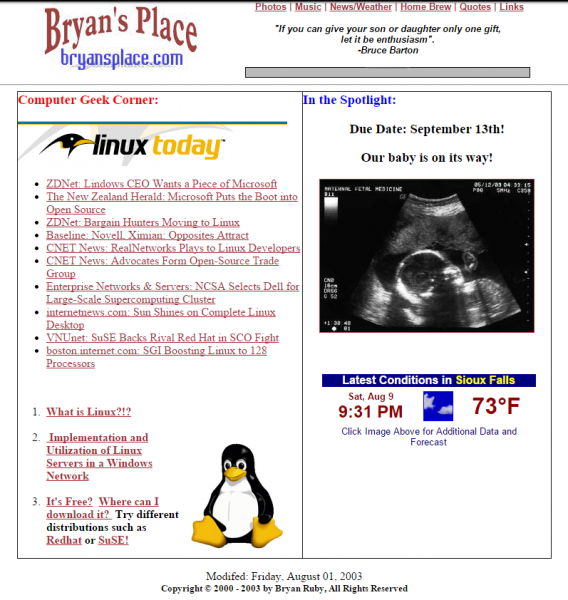
Bryan Ruby: Social Media Killed My Family Website
For the first time in 15 years, my family doesn't have a website to call their own. In January 2000, I registered the domain Bryansplace.com. This was the first website I ever built outside of work and it became a sandbox for me to express my interests as well as a way to seek personal growth. From handwritten HTML pages, a detour with Frontpage, and eventually to a number of CMSs, the software and content at Bryansplace evolved as my life evolved.
Drupal Security: Not Shocking but Responsible
Over the years, I've made it an unwritten policy not to sensationalize bug fixes and security vulnerabilities in content management systems. While there may be great interest in such stories, I believe such stories have a tendency to cause more harm than good. When sensationalized, such articles tend to cause customers to address security concerns with emotion instead of logic which is never a good thing. So, when the security vulnerability known as "Drupageddon" broke and Drupal developer Bevan Rudge posted "Your Drupal website has a backdoor", I knew this story was going to eventually reach mainstream media.
Pagination
- Previous page
- Page 7
- Next page



